Look, a lot of people aren’t going to like what I’m saying here:
If you’re not using a password manager, you should just quit your job in tech.
-Me
UPDATE (28Dec2022): LastPass has had severe security problems and exhibited downright shady obfuscation in following up to a hacking. I no longer recommend them, explicitly recommend AGAINST them and apologize for misreading things previously and recommending them to anyone who was following my advice. Bitwarden seems much better and as an OpenSource provider, problems should be made apparent much faster than was teh case with LastPass.
Humorous lesson: you should also quit any other job with any level of power or authority. Especially if you happen to be a president that wears his Twitter password on a hat.
So, why should you quit any job with any authority? Especially a tech job? Well…
You wouldn’t trust a technology consultant emailing you from a domain like: Yahoo.com or AOL.com. Neither should you trust someone who is relying on some terrible combination of memory, password re-use, or browser password storage.
Why would I make an outrageous claim like “If you don’t use a password manager, you should quit your tech job”? Because not using a password manager when you work in tech is indicative of either professional negligence, professional ignorance or professional laziness.
Your passwords have been breached. I promise. 10 BILLION accounts have been compromised. You can check if yours was among them here (at havibeenpwned.com maintained by security researcher and Microsoft Regional Director Troy Hunt.)
This could be a big, long, blog on how important it is to use a password manager, but lots of people have made videos about that and that’s even more fun to go consume than reading.
Here’s a fun one from Vox Media
Fun! Anyway…
Just use a password manager. I recommend and use Bitwarden– it has a free tier to get started and I don’t get any compensation for recommending them. They are also open source which has great perks to it.
There are lots of very well reviewed ones, here’s the G2 Grid for best of the best:
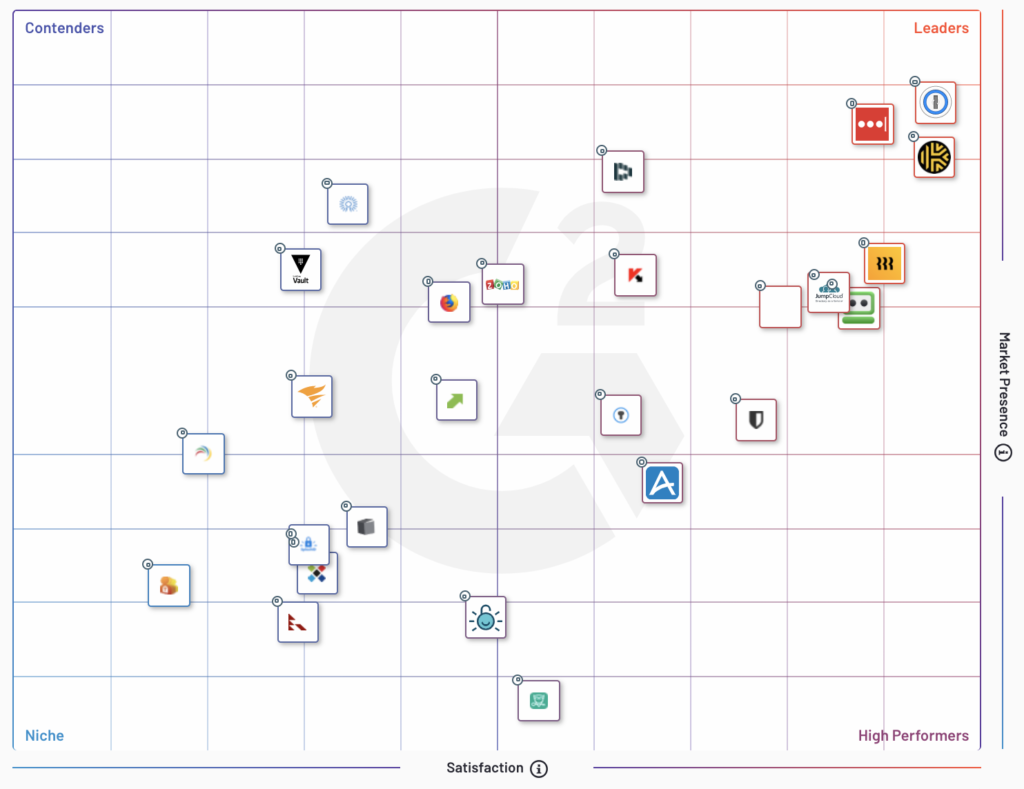
Pick whichever you like from the right hand side…. but you must begin using one, because 2020 was the year of the breaches, and so were all the years before it And 2021 will be too… Just do it. Today. Right now. Stop reading this and start setting up a password manager. Here’s an independent how-to from EFF: a security and privacy non-profit here. Seriously this blog will wait, go do it.
Are you back? Did you do it? Can you keep working in tech- or any position with any level of authority?
Additional updates by request:
Some people have specific questions and asked that I address them. Don’t let concerns delay or dissuade you from making things better. Don’t let an imagined perfect delay you from an implemented improvement.
Question: How do I know I can trust a P-word manager?
Answer: Depends on your threat-model but. Bitwarden (and likely many others encrypt your passwords and your vault on device before transmitting the blob into the cloud for storage and retrieval by other devices whether a mobile device or browser plugin on a laptop. (and if you’re careful, those wont help an attacker because you chose an 8 random word passphrase like we talked about here).
Additional Answer: Read takes by external independent security researchers. Like Steve Gibson, or Brian Krebs , watch how the software provider reacts to security vulnerability disclosures and breaches/attacks.
Question: what about Multifactor (or 2 Factor) Authentication?
Answer: Yes! Use it all. Use MFA to access your password manager vault AND all of the accounts whose passwords it prevents.
Question: But don’t I also need to think of other things too? Like password reset questions? Re-use of login-IDs and so on?
Answer: Yep – if possible generate passwors for usernames if they’re allowed to be anything and make your password reset questions untrue at least, ideally generate new passwords for those and save them as notes in your file for that account on….your password manager! Or if you must have a robust backup print them out and put them in a safe along with your password to access your password manager and 2 or MFA seeds and recovery items.
Question: but… but.. but…
Answer: Security is a process not a product. There is no perfect solution out there for you, nothing will fix it all for you. If you are not using a password manager your answer better be one of these 3:
1.) I am a hacker and I use my own open source security password management software hosted in encrypted cloud plausible deniability drives, secured by strong passphrases I have memorized and do not re-use, in combination with several MFA including hardware keys
2.) I do, but there are some passwords I cant use it for (government systems etc that wont allow installation of PW manager software)
3.) I’m sorry, I’m starting today
Comments
One response to “If you don’t use a password manager, you should quit your tech job…or any job.”
[…] hasling friends and family about security and online security for about as long as I can remember. Ive written some harsh posts about it. I’ve even been very lucky to co-found and advise a startup that makes it easy for developers […]